Vulnerability Management
When I joined Cast AI, there was already a vulnerability management product in place. It looked fine on the surface — detailed insights, plenty of data. But something felt off. Security workflows rarely belong to a single role. Developers build the applications, DevOps teams manage infrastructure, and security teams monitor risk and coordinate remediation. Yet the product was designed broadly for everyone — which in practice meant it wasn't really working for anyone.
Introducing Personas
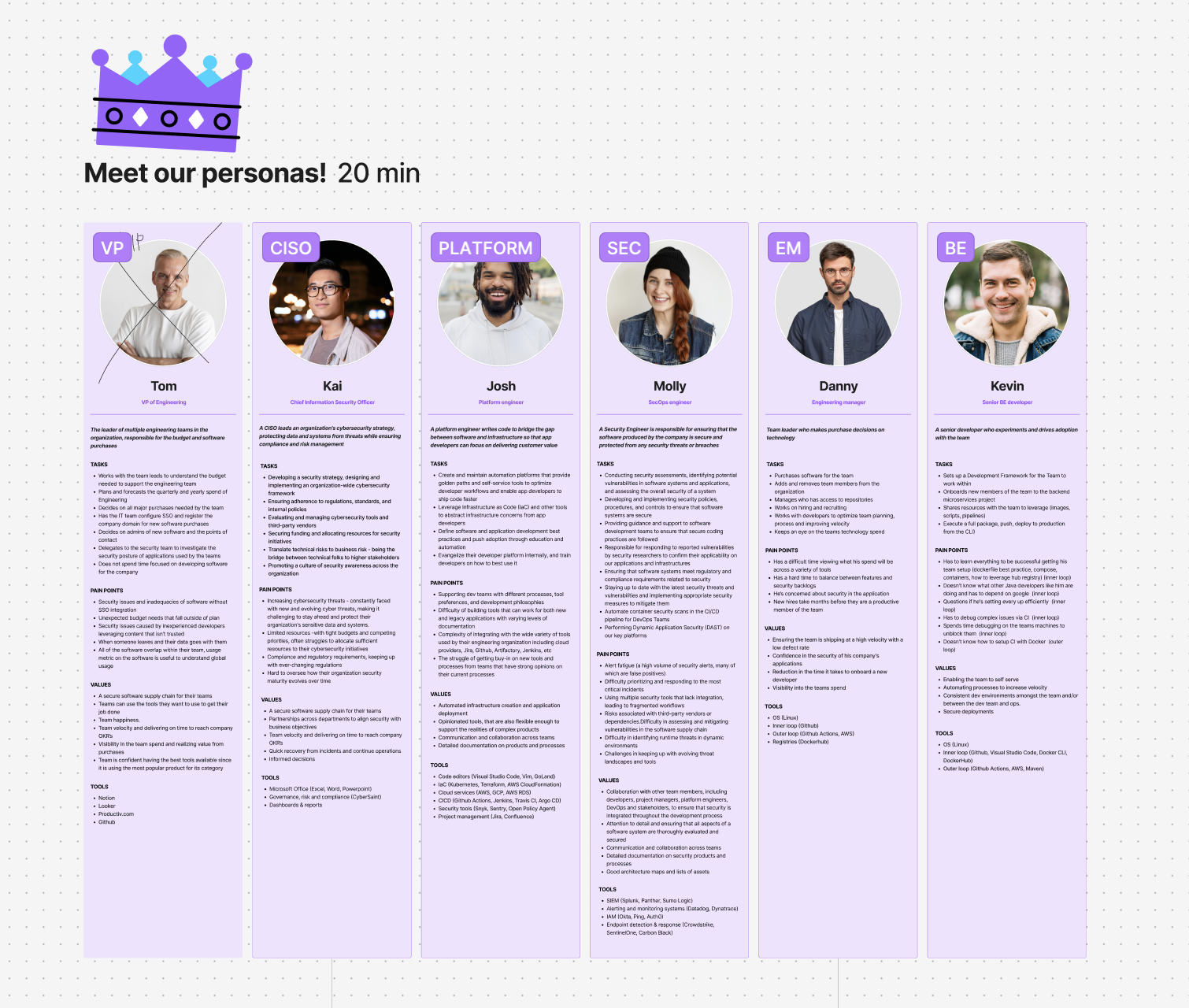
To bring some clarity, I organised a persona and user journey workshop with the team. Rather than starting from scratch, I dusted off personas previously used in other security products and refreshed them to fit Cast AI's context. The team had already spoken with a lot of users, so they could bring real stories and observations to the table.
The goal wasn't to produce documentation — it was to get everyone aligned. Once we had shared personas, the team started speaking the same language about users. That alone changed how we talked about the product.
Understanding Collaboration
Once we had the personas in place, the next question was a natural one: how do these people actually work together when something goes wrong? A vulnerability doesn't get fixed by one person sitting alone, security incidents require coordination between multiple teams. SecOps spots the risk, developers assess the impact on the application, platform engineers look at the infrastructure side. So we mapped that full journey, from the moment a vulnerability is discovered all the way through to resolution. Seeing it laid out made it obvious where the experience was breaking down.
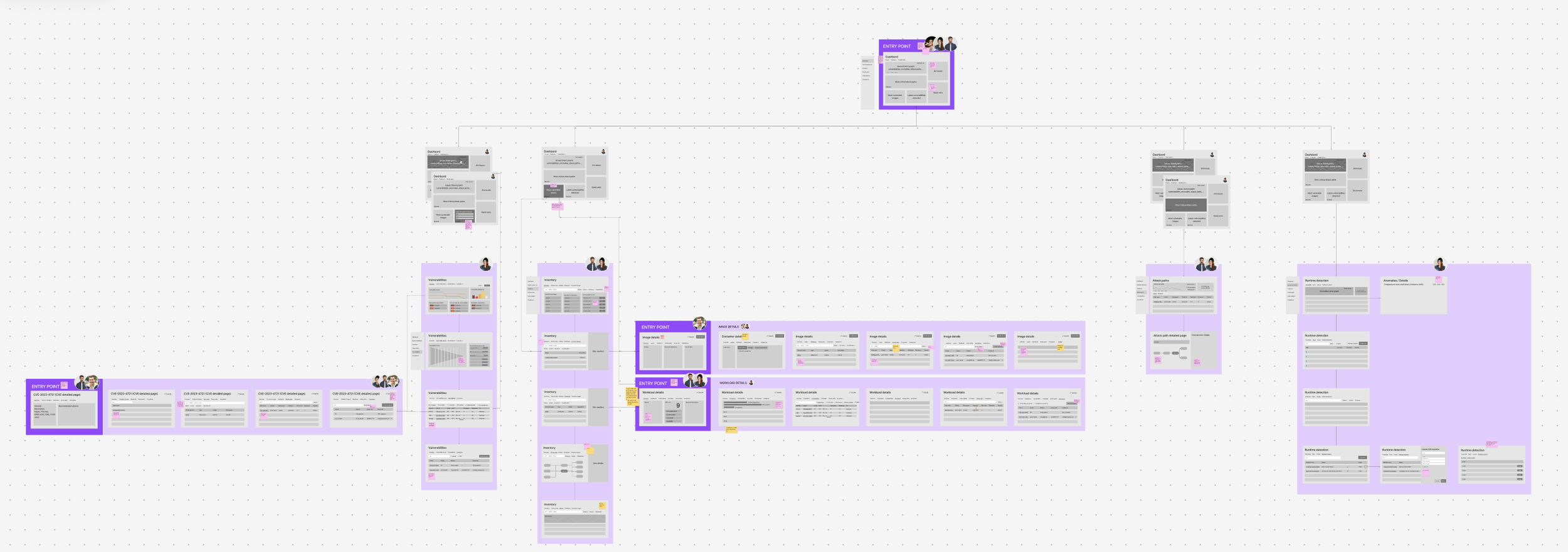
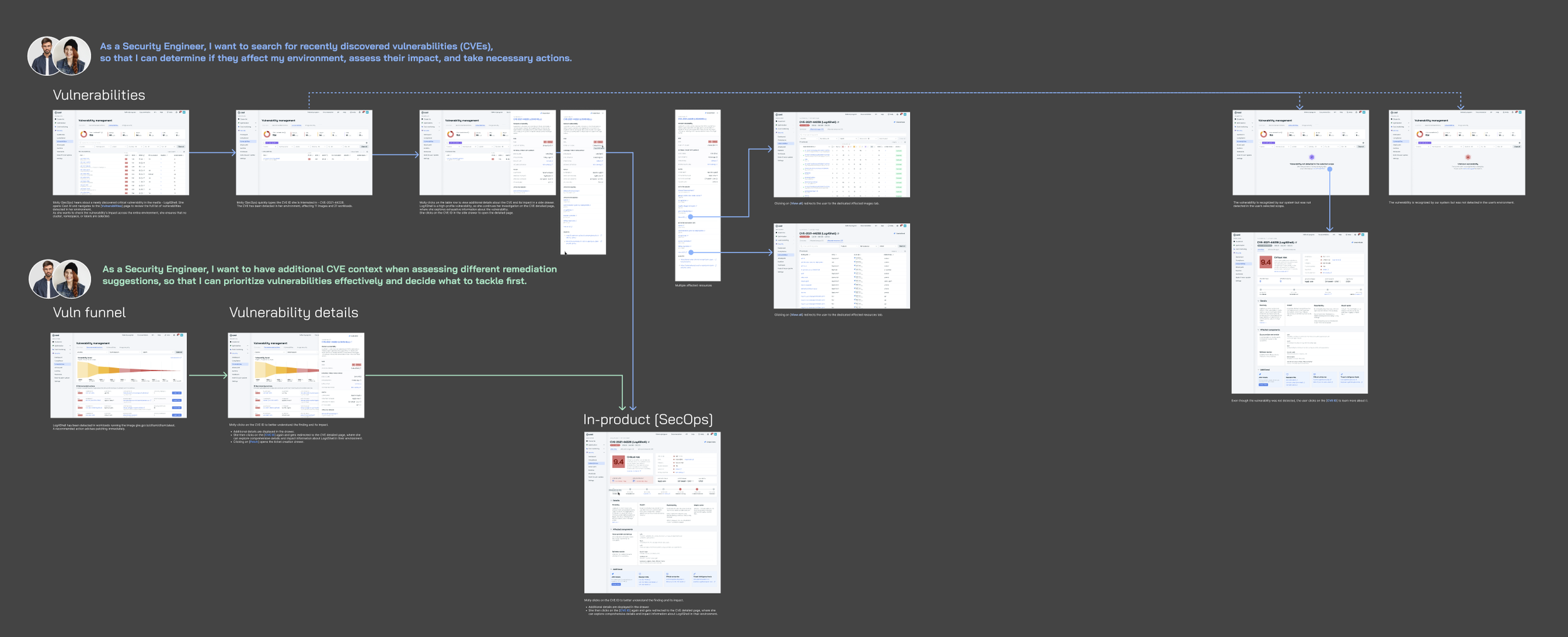
Exploring the Product Vision
With the personas and journeys as our foundation, we started thinking bigger — what should this product look like in the long run? We took the features on the roadmap and tried to illustrate how they could come together into a coherent vision. Using rough thumbnail sketches of pages, we explored the overall structure, figured out the right entry points for each persona, and mapped how different roles would navigate the product depending on their goals. Small, scrappy, fast — just enough to get everyone looking at the same picture before committing to anything.
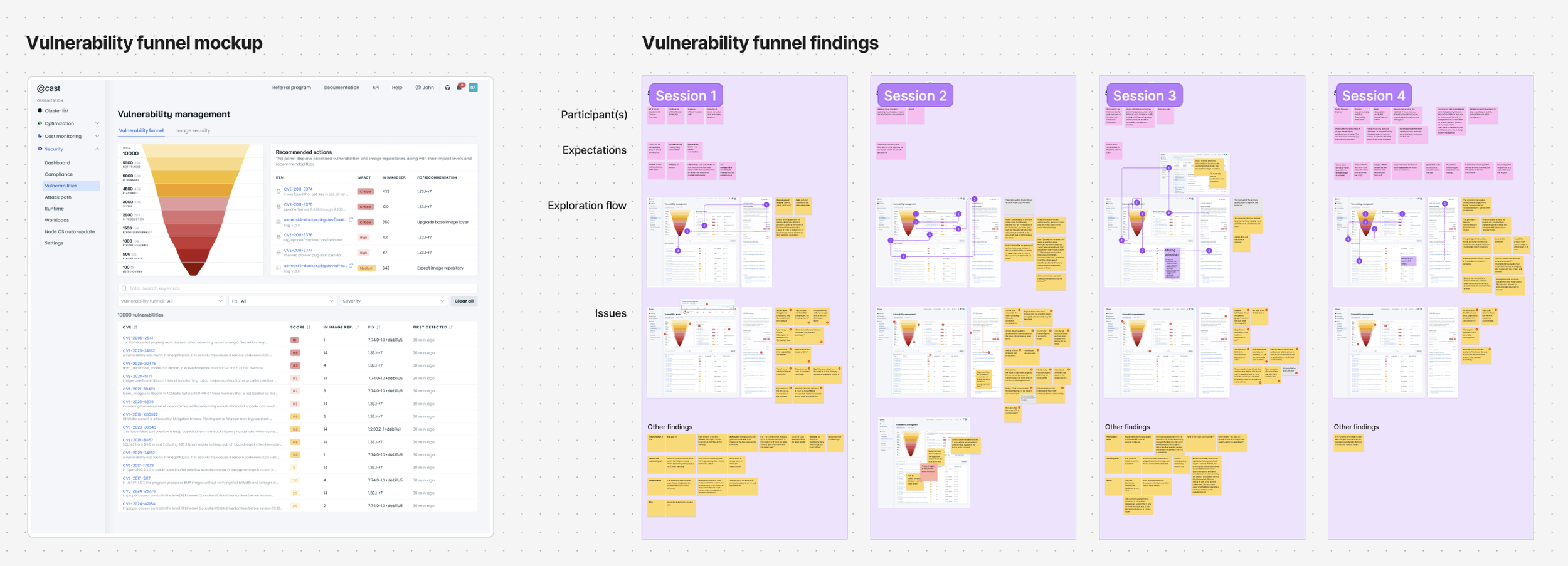
validation
To validate our assumptions, I ran a series of usability sessions focused on the existing vulnerability funnel. Participants interacted with the product while approaching tasks from their own role's perspective. This helped us understand how different users interpreted vulnerability data and what they needed to move forward. The sessions revealed both usability issues and deeper workflow gaps — and along the way, uncovered user needs we hadn't previously considered.
Redesigning the Experience
Using these insights, we redesigned the vulnerability management flow to support a more structured investigation process. The new experience gave SecOps users the context they needed to understand and evaluate vulnerabilities on their own first — before looping in engineering teams. From there, they could kick off investigations and collaborate with developers and platform engineers to figure out the best path forward.
Outcome
The redesigned experience created a clearer path from vulnerability discovery to resolution. SecOps users could now investigate vulnerabilities with confidence, while developers and platform engineers were brought in at the right moments — not too early, not too late. Most importantly, the product finally reflected how security work actually happens: through collaboration across teams.